Cybersecurity can be an intimidating word but not if you have a firm grasp of the basics. You don’t need to be a techie to get it right. All it takes to protect yourself from the most prevalent attacks are a few common sense precautions. So grab your device, go through this list and check them off one by one. I promise it won’t take long. Check these 6 easy steps to Protect Your Android Device from below.
1) Get a secure lock screen right now
This one is so obvious it almost hurts to write but there are still people who don’t have lock screens. Setting one should be the very first thing you do when you get a new phone. With the latest Android models, you can choose from several options: fingerprint scan, voice recognition, pattern, PIN or password. Traditional PIN and password, however, seem to remain the safest options for now (as long as your PIN isn’t 1111, of course).
2) Quit using the same password for all accounts
There are two main mistakes people make when setting passwords. They usually go for things that are easy to remember: a pet’s name or a loved one’s date of birth. Secondly, they tend to use one or two passwords for all their accounts. Unfortunately, both behaviors greatly increase the risk of cyber attacks.
If you don’t want to fall prey to hackers, it’s essential to use a password generator for producing high-security unique passwords. They consist of a random string of letters, numbers, and characters that is indefinitely harder to crack them a typical one-word password. You also need to set a different password for each and every account. Data leaks are much more common than you think – if your Facebook password gets out, you don’t want to give hackers the key to all your other accounts, do you?
Of course, a random string of numbers and characters from a generator is impossible to remember. That’s why you need a password manager, such as 1Password, KeePass or LastPass, to securely store all your passwords in one place. Before you pick the master key for your password manager, check if that password has been exposed in a data breach here: https://haveibeenpwned.com/Passwords
3) Enable two-factor authentication on Google
Is your Google account constantly prompting you to enable two-factor authentication? Yes? That’s because it’s really important! Two-factor authentication is an extra layer of security for all your Google apps. Even if a hacker gets access to your password (maybe it was exposed in a data breach, for example), they still need to go through phone authentication to log in. That’s not impossible but it’s definitely more difficult to do.
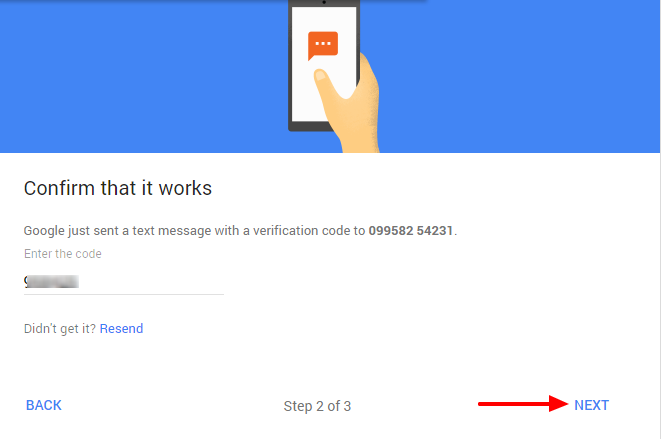
Two-factor authentication is ridiculously easy and only takes a couple of minutes so there’s no excuse. Got to your account settings page and find the “Security” section. Under “Signing in to Google”, you’ll see “2-Step Verification”. Follow the link – the process is straightforward and simply asks you to enter your phone number and then confirm it by entering a code from a text message. Easy peasy.
4) Only download apps from trustworthy sources
Some apps are just a clever cover-up for sneaking malware onto your device. A legitimate-looking free game or sleep tracking app could contain a Trojan virus that hackers use to spy on you and steal sensitive information.
To avoid harmful apps, always download software from trusted sources, like Google Play. Google Play runs apps through a verification process to make sure they’re safe. If you have some apps on your device you’re unsure about, you can use Play Protect, Android’s in-built malware detection, to scan them for viruses.
5) Find a reliable VPN
As soon as your device connects to Wi-Fi, it’s exposed a whole new world of cyberthreat. It takes little effort to spy on your browsing information, especially if you’re using a public network. Open Wi-Fi is often generally unencrypted so anyone sitting in the same café could be snooping on your online activity to steal your passwords or other sensitive information.
Luckily, the solution is easy enough – an Android VPN helps curb online risks by encrypting your internet traffic. VPN, short for a virtual private network, routes your traffic through a virtual encrypted tunnel before anyone, even your Internet Service Provider, can see it. That means that even if the attacker is intercepting your traffic, they only see encrypted information and not raw data so. They can’t easily determine what websites you’re visiting, what you’re doing there and what passwords you’re entering.
Unfortunately, finding a good VPN app can be tricky. After VPN’s surge in popularity, the market was flooded with fake or malicious apps which either don’t work properly or actively collect your data for profit. The operational costs of maintaining a VPN service are high so you should use common sense and steer clear of free products – always ask yourself “What’s the hidden cost of this app” before you download it.
A good rule of thumb for VPN is to do some research before you commit. Read the terms and conditions to see if the provider is collecting your data and check app permissions for anything suspicious. A reliable VPN for Android shouldn’t need access to your microphone nor should it be storing your browsing data.
6) Check app permissions
Let’s face it. When you download an app and it shows you a long list of access permissions, you probably just tap away as fast as possible to get to your new app. A lot of the time, however, those access permissions are excessive and unnecessary: a game doesn’t need to read your texts and a fitness app doesn’t require access to your microphone to work.
If you don’t read the access permissions carefully before you click “agree”, you should go back and manually turn off anything that looks suspicious for all apps you have installed. Simply head over to settings and click on “Apps” or “Application manager”. You can control which apps are allowed to do what by tapping on an individual app and changing access under “Permissions”.
Wrapping Up
These are the best ways to Protect Your Android Device. If you concern about your device security and your privacy, you should follow the above steps.